Abnormal AI Review What Security Teams Should Know
Email remains one of the most exploited attack surfaces in modern enterprises. Despite secure email gateways and employee training, phishing, business email compromise, and social engineering attacks continue to bypass traditional defenses.
Security teams across the United States, United Kingdom, Canada, and Australia face a growing challenge. Attackers are using more sophisticated tactics powered by automation and artificial intelligence. Legacy rule based systems are no longer enough.
This is where abnormal ai enters the conversation.
In this abnormal ai review, we explore how the platform protects organizations from advanced email threats by analyzing behavior rather than relying solely on static rules or signatures. The tool is designed to detect anomalies in communication patterns and stop attacks that appear legitimate on the surface.
The problem it solves is critical. Modern phishing campaigns are highly personalized. They often mimic trusted contacts and exploit human psychology. Abnormal ai focuses on identifying deviations in behavior to block these threats before they cause damage.
It is built for enterprise security teams, CISOs, IT administrators, and compliance leaders who require proactive email protection without increasing operational complexity.
What Is Abnormal AI
Abnormal Security is the company behind abnormal ai, a cloud native email security platform that uses behavioral AI to detect and prevent advanced email attacks.
Abnormal ai integrates directly with cloud email providers and analyzes communication patterns across an organization. Instead of depending on predefined rules, it builds a baseline of normal behavior for users, vendors, and executives. When anomalies appear, such as unusual payment requests or suspicious login patterns, the system flags or blocks the message.
Within the broader cybersecurity SaaS landscape, abnormal ai operates in the email security and threat detection segment. It competes with secure email gateways and advanced threat protection platforms but differentiates itself through behavioral analysis and AI driven detection.
For new readers, abnormal ai can be understood as a behavioral intelligence layer that sits on top of existing email infrastructure, strengthening defenses against modern social engineering attacks.
How Abnormal AI Works
Understanding how abnormal ai works helps security teams evaluate fit and effectiveness.
Step One Integration With Email Environment
The platform integrates with cloud email services such as Microsoft 365 and Google Workspace. Deployment is typically API based, which reduces the need for complex infrastructure changes.
Step Two Behavioral Baseline Creation
Abnormal ai analyzes historical email data to understand normal communication patterns. This includes who communicates with whom, writing style, tone, frequency, and transactional behaviors.
Step Three Real Time Threat Detection
Incoming emails are evaluated against behavioral baselines. If a message deviates significantly, such as an unusual wire transfer request from a spoofed executive account, it is flagged or quarantined.
Step Four Automated Response And Remediation
Security teams can automate response workflows. Suspicious emails can be removed from inboxes organization wide, reducing dwell time and exposure.
Step Five Continuous Learning
The platform continuously refines its models based on new data and threat patterns. This adaptive approach strengthens detection over time.
The daily workflow for security teams is streamlined. Instead of manually reviewing large volumes of alerts, teams focus on high confidence threats surfaced by behavioral analysis.
Core Features Overview
Abnormal ai delivers targeted capabilities designed for modern email threat defense.
Behavioral AI Detection
The core feature is behavioral modeling. By learning how users typically communicate, the system identifies subtle anomalies that traditional filters miss.
Why it matters: Advanced phishing attacks often appear legitimate. Behavioral context adds a critical layer of detection.
Business Email Compromise Protection
The platform specifically addresses business email compromise, which is one of the most financially damaging cyber threats.
Why it matters: Financial fraud through email can result in significant losses and reputational damage.
Automated Incident Response
Security teams can automate investigation and remediation steps. This reduces manual workload and accelerates containment.
Why it matters: Faster response times reduce risk and operational strain.
Account Takeover Detection
Abnormal ai monitors for unusual login behavior and suspicious account activity.
Why it matters: Early detection of compromised accounts prevents lateral movement and further exploitation.
Each feature addresses a real world security challenge faced by enterprise organizations.
Key Benefits For Users
Security leaders evaluate platforms based on risk reduction and operational efficiency.
Reduced False Positives
Behavioral intelligence can decrease alert fatigue by focusing on meaningful anomalies rather than generic keyword triggers.
Faster Threat Containment
Automated remediation capabilities allow organizations to remove malicious emails quickly across the enterprise.
Improved Financial Risk Protection
By targeting business email compromise, abnormal ai helps protect against fraudulent transactions and vendor payment scams.
Seamless Cloud Integration
API based deployment minimizes infrastructure disruption.
Scalable Protection
As organizations grow, the platform scales with user volume and communication complexity.
The result is stronger email security without significantly increasing headcount or operational overhead.
Who Should Use This Software
Abnormal ai is designed primarily for mid to large enterprises with cloud based email environments.
Chief Information Security Officers
CISOs seeking advanced protection against social engineering attacks will find the platform aligned with strategic risk management goals.
Security Operations Teams
SOC teams benefit from reduced alert fatigue and automated remediation workflows.
Financial Institutions
Organizations handling high value transactions require strong business email compromise defenses.
Healthcare And Professional Services
Industries that manage sensitive data and client communications benefit from behavioral detection capabilities.
Smaller organizations may also benefit, but the platform is particularly impactful in complex environments with high communication volumes.
Use Cases And Real World Scenarios
Practical scenarios illustrate abnormal ai in action.
Scenario One Executive Impersonation
An attacker sends an email impersonating a CEO requesting an urgent wire transfer. The message appears legitimate. However, abnormal ai detects subtle differences in tone and context compared to previous communications. The email is quarantined before reaching the finance team.
Scenario Two Vendor Payment Fraud
A supplier email account is compromised. The attacker requests updated bank details for future payments. The system identifies the anomaly in payment behavior and flags the request for review.
Scenario Three Account Takeover
Unusual login activity is detected for an employee account. Abnormal ai alerts the security team, enabling immediate password resets and investigation.
In each case, the value lies in proactive detection rather than reactive cleanup.
User Experience And Interface
Security software must provide clarity under pressure.
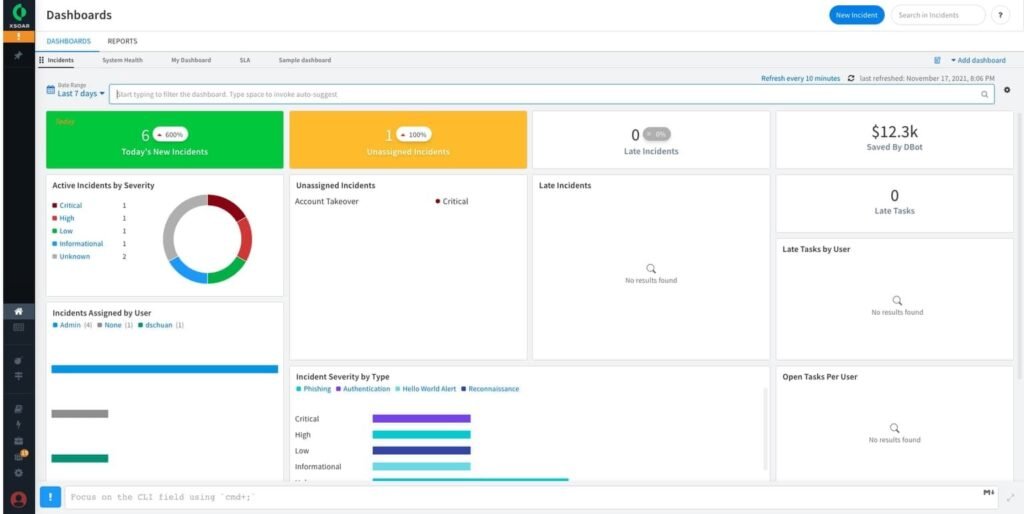
Abnormal ai offers a centralized dashboard where security teams can view detected threats, behavioral insights, and remediation actions. The interface is structured to highlight high risk incidents.
Navigation is designed for efficiency. Security analysts can quickly investigate flagged emails and understand why they were identified as anomalous.
The learning curve is moderate. Security professionals familiar with email threat analysis adapt quickly. The platform emphasizes actionable insights over excessive technical noise.
Accessibility features such as clear reporting and exportable logs support compliance and audit requirements.
Pricing And Plans Overview
Enterprise security platforms typically offer customized pricing based on user count and feature requirements.
Abnormal ai generally structures pricing around the number of protected mailboxes. Larger deployments may include advanced features and dedicated support.
Organizations should evaluate pricing in relation to potential loss prevention. The cost of a single successful business email compromise incident can exceed the annual subscription fee.
A proof of concept or pilot deployment can help validate effectiveness before full scale adoption.
Pros And Cons
A balanced abnormal ai review requires transparency.
Pros
Advanced behavioral detection
Strong protection against business email compromise
API based cloud deployment
Automated remediation capabilities
Reduced alert fatigue
Cons
Primarily focused on email threats
May require budget allocation at enterprise level
Best suited for cloud based email environments
For organizations seeking comprehensive endpoint or network protection, additional tools may still be required.
Comparison With Similar Tools
Abnormal ai competes with solutions such as Proofpoint and Mimecast.
Proofpoint offers a broad range of email security and threat intelligence services. It has strong enterprise presence and extensive feature sets.
Mimecast provides email security, archiving, and continuity services with integrated protection layers.
Abnormal ai differentiates itself through its focus on behavioral AI and anomaly detection. Rather than relying heavily on predefined rules or signature based scanning, it builds dynamic communication models.
Organizations evaluating options should consider existing infrastructure, integration requirements, and desired level of automation.
Buying Considerations For Decision Makers
Before adopting abnormal ai, security leaders should evaluate several factors.
Existing Security Stack
Assess how the platform integrates with current email security solutions and SIEM systems.
Risk Exposure
Organizations handling high value financial transactions or sensitive data may prioritize advanced behavioral detection.
Budget Allocation
Consider total cost relative to potential financial and reputational loss from successful attacks.
Compliance Requirements
Ensure the solution supports logging, reporting, and regulatory standards relevant to your industry.
Reviewing documented SaaS security case studies can help demonstrate measurable risk reduction and operational efficiency improvements.
Security Privacy And Compliance
As a security platform, abnormal ai places strong emphasis on data protection.
The system analyzes email metadata and content patterns to detect anomalies. Organizations should review data handling practices, encryption standards, and access controls.
Compliance alignment with regional and industry regulations is essential, particularly for financial services and healthcare sectors.
Security transparency builds trust with enterprise buyers who require assurance regarding data residency and governance.
Support And Documentation
Enterprise adoption depends on reliable support.
Abnormal ai provides onboarding assistance, documentation, and customer support channels. Organizations should confirm availability of dedicated support and service level agreements.
Clear documentation helps security teams maximize platform effectiveness and streamline internal training.
Post deployment support is critical in maintaining confidence during high pressure security incidents.
Final Verdict
This abnormal ai review highlights a focused and modern approach to email security. By leveraging behavioral AI, the platform addresses one of the most persistent and costly enterprise threat vectors.
Its strengths lie in advanced anomaly detection, automated remediation, and strong protection against business email compromise.
Abnormal ai is best suited for mid to large enterprises with cloud based email environments and a need for proactive social engineering defense.
Organizations seeking broader cybersecurity coverage will still require complementary tools. However, for email specific threat protection, abnormal ai represents a strong strategic investment.
Frequently Asked Questions
Is Abnormal AI Suitable For Small Businesses
It is primarily designed for enterprises and mid sized organizations with cloud email systems.
Does Abnormal AI Replace Existing Email Gateways
It typically works alongside existing solutions, adding behavioral intelligence rather than fully replacing all security layers.
Can Abnormal AI Detect Business Email Compromise
Yes. Protection against business email compromise is one of its core strengths.
Is Deployment Complex
Deployment is generally API based, which reduces infrastructure changes in cloud environments.
Does Abnormal AI Scale With Organizational Growth
Yes. The platform is designed to scale as mailbox counts and communication volumes increase.

